Messages telling you to install and update security software for your computer is a scary message.
This tactic is known as scareware: http://en.wikipedia.org/wiki/Scareware
Related article about "Free Security Scan" alerts from the Federal Trade Commission
Court Halts Bogus Computer Scans
"Free Security Scan" Could Cost Time and Money

Since several months ago, massive attacks (obfuscated javascript inserted - IFRAME to inject backdoors/keyloggers), thousand of hacked websites used to distribute rogue antivirus have been detected by major antivirus vendors, cyber intelligence labs and other security companies.
The exponential growth of rogue antivirus distribution through legitimate websites remain silent as the tactic used by the creators continued to become more sophisticated.
Related article: Scammers making '$15m a month' on fake antivirus
PandaLabs: 22,000 New Malware Samples Detected Every Day in 2008
PandaLabs Annual Report
| Rogue AV Detections in 2008 |
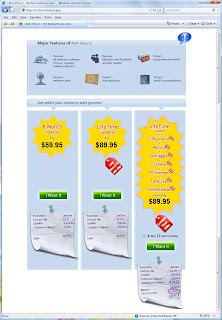
Sites on this blog refers to rogue antispyware which display misleading scan alerts and mostly installed on computer's victim without user consent throught infected websites (LEGITIMATE infected websites).
UPDATE:
The site now include IPs / botnet C&C / data logs exposed, links to LIVE urls exploits/vulnarabilities (flash - pdf) and domains with their relations, route, AS and malicious scripts found on
compromised websites related to the same campaign.
If you arrived to this page through a search engine about a domain in this blog, some removal information can be found on the links below. Sites analysis will be created and updated as new sites will be found. Twice or more a day if needed.If you arrived to this page and you are interested to find some information about these attacks,
IPs domains and networkd used, here are some links used with details about this malware campaign
Related article:
Black Hat SEO and Rogue Antivirus: Rogue Fake SpyGuard Malware Defender 2009
Black Hat SEO and Rogue Antivirus: Fraudulent payment processors Antivirus360
Black Hat SEO and Rogue Antivirus: Fake Scanner RapidAntivirus templ. AntivirusPlus
Black Hat SEO and Rogue Antivirus: WinWebSecurity InternetAntivirusPro
Black Hat SEO and Rogue Antivirus: ZlKon Malware Drop
Black Hat SEO and Rogue Antivirus: AntiSpyware Pro 2009
Black Hat SEO and Rogue Antivirus: Rogue Fake SpyGuard
Black Hat SEO and Rogue Antivirus: WinWebSecurity InternetAntivirusPro
Black Hat SEO and Rogue Antivirus: WinWebSecurity InternetAntivirusPro new variants
Black Hat SEO and Rogue Antivirus:
Part. 1) Black Hat SEO and Rogue Antivirus
Part. 2) Black Hat SEO and Rogue Antivirus: The World Wide Web Consortium Mystery
Part. 3) Black Hat SEO and Rogue Antivirus: AntivirusPlus ZlKon and liveinternetmarketingltd.com
Part. 4) Black Hat SEO and Rogue Antivirus: Full or Rogues
Part. 5) Black Hat SEO and Rogue Antivirus: Full of Hacks
Part. 6) Black Hat SEO and Rogue Antivirus: Analyzing the tactic p.1
Part. 7) Black Hat SEO and Rogue Antivirus: Analyzing the tactic p.2
Part. 8) Black Hat SEO and Rogue Antivirus: Fake AV + Rootkit TDSS / Alureon / DNSChanger
Black Hat SEO - Exploit, scripts, botnet C&C, hacks toolkit etc.
Part. 1) Black Hat SEO - Botnets, Scripts, Exploits, Hacks: Thousand of domain attacked
Part. 2) Black Hat SEO - Cyber Crime Toolkit Exposed: Welcome to LuckySploit:) ITS TOASTED
Part. 3) Black Hat SEO - Botnets, Scripts, Exploits, Hacks: Triple threats
Part. 3) Black Hat SEO - Botnets, Scripts, Exploits, Hacks: Crimaware toolkits in the wild
And here we have a list of fake scanner websites used in the attack which infect thousand of websites to distribute malware also known as WinWebSec (WinWebSecurity or SystemSecurity2009): Black Hat SEO and Rogue Antivirus
Note:
Other rogue av like AntivirusPlus through this list has been detected recently
Many more like under the name of FakeSpyGuard, VirusRemover, WinAntiVirus2008, SpywareRemover2009, and some variant of "Trojan Hiloti" through this list
Similar attacks with Google search strings :
In 2008: We have an example with "Antivirus 2009" on the Trend Micro Malware Blog:
A Million Search Strings to Get Infected
A few days ago: On the CA website "onlinestabilityworld.com" is cited. The article is here:
Rogue Security Software keeps on hitting Google searches
Another list of fake codec websites in March on the Dancho Danchev's blog alsocited on this blog
Bogus LinkedIn Profiles Redirect to Malware and Rogue Security Software
And recent search also reveal the use of a powerfull javascript library jQuery - the screenshot below has been retreived from a legitimated infected website.
Deobfuscated result is:

The ip is 94.247.2.195 (ZlKon)
Network used for hosting these malicious website are
Starline Web Services in Estonia
Zlkon in Latvia
netdirekt e.K. in Germany
Hetzner Online AG in Germany
Ural-NET in Russia
Eurohost LLC in Ukraine
GloboTech via Olexij Khrenov in Ukraine
Joint Multimedia Cable Network in Ukraine
NTColo Networks in Ukraine
Plitochnik Lux LTD in Ukraine
Coloquest in US
Netelligent Hosting Services Inc in US
and some other in China, Moldavia.
IPs, AS and network used can be found on this blog.
-------------
New sites used
on March 28: slot4scan.com, scan4fuse.com, list4scan.com, scan4home.com, gotimescan.com
on March 29: mainscan6.com, scan4plus.info, scan4open.com
on March 30:
logscan6.com
scan4way.com [redirection by gostepscan.com]
5scanav.com and scan5plus.com [redirection by gowithscan.com]
new4scan.info,scan4live.info
April:
best4scan.info, best6scan.info,pro4scan.info,scanline6.com, scan6log.com, scan6main.com, scan6now.com,zpmuwbtqqwkw.net
Analysis here
-------------
Related article: The rash of rogue av (PDF)
Related article about McColo Business:
Similar network at UltraNet Ltd in Lavtia
HostExploit’s Cyber Crime Series (PDF)The list on your right hand side are latest websites used in this malware campaign. (Updated daily)
Some interesting links about malicious traffic at DATORU EXPRESS SERVISS - ZlKon in Latvia
Pages related to the same attack. (Included some other problems, SPAM, botnet etc...)
December 15, 2008:
FakeAV and Codecs
http://realsecurity.wordpress.com/2008/12/15/sources-of-badness-zlkon/
December 19, 2008:
SPAM IP Detected
http://forums.pligg.com/general-help/16374-spam-ip-94-247-2-29-kill.html
http://www.projecthoneypot.org/ip_94.247.2.29
McAfee Avert Labs Blog
Monday January 5, 2009
Explanation of the so-called “Traffic Management System” - Inside The Malicious Traffic Business
http://www.avertlabs.com/research/blog/index.php/2009/01/05/inside-the-malicious-traffic-business/
We also have an complete example here. From the visitor to the legitimate infected website (with logs, screenshot, ips and analysis of the malicious website as well as the technic used. i.e: SUTRA traffic redirection, PDF exploit to inject backdoors etc..)
Zeus Tracker
https://zeustracker.abuse.ch/monitor.php?host=94.247.3.211
Wednesday January 7, 2009
Google Code Project Abused by Spammers
http://www.avertlabs.com/research/blog/index.php/2009/01/07/google-code-project-abused-by-spammers/
January 19, 2009
Inaccurate whois details
http://msmvps.com/blogs/spywaresucks/archive/2009/01/21/1663955.aspx
January 2009
http://voices.washingtonpost.com/securityfix/2009/01/troubled_ukrainian_host_sideli.html
Paragraph:Sunbelt's Jordan said those responsible for DNSChanger appear to have begun moving to a new base of operations over the past few weeks, to a network in Latvia, called "Zlkon.lv."
http://ddanchev.blogspot.com/2009/02/diverse-portfolio-of-fake-security.html
http://ddanchev.blogspot.com/2009/02/template-ization-of-malware-serving.html
Paragraph from the ddanchev.blogspot.com:
Interestingly, within the mirrored copy now tweaked and distributed for free using free image hosting services as infrastructure provider for the layout, there are also leftovers from the original campaign template that they mirrored - which ultimately leads us to DATORU EXPRESS SERVISS Ltd (AS12553 PCEXPRESS-AS) or zlkon.lv In the wake of UkrTeleGroup Ltd's demise -- don't pop the corks just yet since the revenues they've been generating for the past several years will make it much less painful -- a significant number of UkrTeleGroup customer, of course under domains, have been generating quite some malicious activity at zlkon.lv for a while.
January 25, 2009
Rogue software - FakeAV
http://pandalabs.pandasecurity.com/archive/New-Rogue_3A00_-Total-Defender.aspx
February 5, 2009
Similar attack with the same added code between like <!-- ad --> <!-- /ad -->
(Same code here)
http://www.aladdin.com/AircBlog/post/2009/02/The-latest-undetected-malweb-by-RBN.aspx Other: http://www.aladdin.com/AircBlog/post/2009/02/Iraq's-embassy-in-Tehran-website-compromised-by-hackers.aspx
Wednesday February 25, 2009
Google Trends Abused to Serve Malware
http://www.avertlabs.com/research/blog/index.php/2009/02/25/google-trends-abused-to-serve-malware/
|






























 Active attacks: LATEST ADDITIONS
Active attacks: LATEST ADDITIONS